Cheat Sheet: Agentic Identity Owner Discovery
A key capability for developing life cycle management governance
The What
In early 2025 The Cyber Hut released a discussion-focused article on the “Laws of Identity Security”. The idea behind this was to create interest around what identity security is and how we can start to pragmatically approach the security controls and architectural design stages.
Law 3 in that series was: “Every digital identity (human and non-human) must resolve to a carbon physical person who is accountable for it”.
As AI agents proliferate — often outnumbering human identities by 50:1 or more — the ability to trace every agent back to a responsible human owner is foundational to governance, incident response, compliance, and risk management. Without it, organisations face ‘ghost agents’ with active privileges and no accountability.
Agents need accountability yes, but they also need to be strategically managed as part of a life cycle. That life cycle in turn needs to be linked to a human life cycle for completeness.
The Why
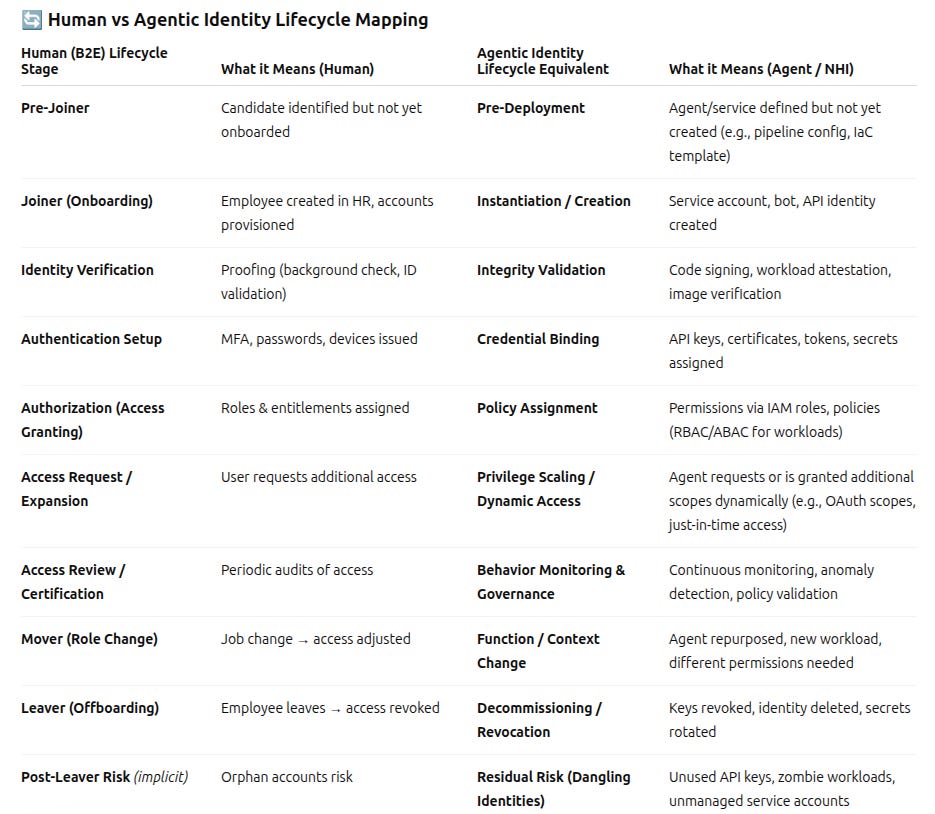
The human B2E employee life cycle can be quite well defined. A basic Google search (or other) will likely generate something like the following:
Joiner (Onboarding)
Creation of the digital identity from an authoritative source (HR system)
Account creation + initial access provisioning
Often automated for Day 1 readiness
Identity Proofing & Verification
Ensuring the person is who they claim to be
Background checks, document validation, etc. (more critical in high-assurance roles)
Authentication Setup
Credential issuance (passwords, MFA, passkeys)
Binding user to authentication methods/devices
Authorization / Access Provisioning
Assigning roles, groups, entitlements
Based on RBAC/ABAC policies (least privilege principle)
Access Request & Approval
Ongoing process where users request additional access
Workflow-driven approvals (manager, app owner, etc.)
Access Review & Certification
Periodic audits of user access (compliance-driven)
Managers/app owners validate “who still needs what”
Mover (Role Change / Lifecycle Update)
Adjusting access when a user changes role, department, or project
Prevents privilege creep
Leaver (Offboarding / Deprovisioning)
Timely removal of access when a user leaves
Includes account disablement, session termination, and cleanup
Now clearly, each of those stages will also have sub-life cycles too. Especially for things like credential management and and issuance. Of course, many organisations struggle to automate these components and are faced with issues such as:
Orphan accounts - no longer linked to a real identity
Ghost accounts - never linked to a real identity
Excess Permissions - assigned versus used out of sync
So what? Well we now need to consider an equivalent agentic life cycle - even if that world is relatively new in comparison.
An example life cycle model for agents could look something like the following:
The management of the agentic life cycle is going to require some different approaches and likely tooling to that of the human world. That is out of scope for this cheat sheet however.
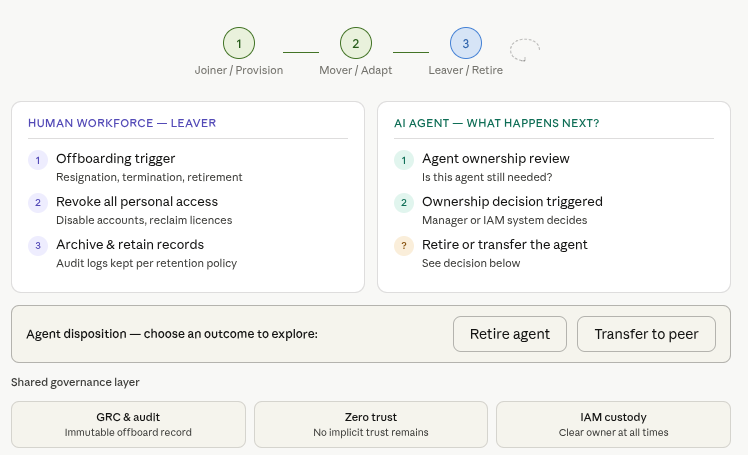
What becomes clear though, is that we need to link the agentic life cycle with the human one. Agents do not and cannot live in a vacuum.
Capabilities
We are now presented with several issues:
How to find an owner for agents already live that are orphaned
How to assign ownership during agent creation in a way that doesn’t inhibit development
How to enforce life cycle changes for humans and agents together
A few ways seem to exist with respect to how this could be done.
AI/ML correlation — analyses logs, code commits, device telemetry, or behavioural signals to infer the likely human owner.
Blended/delegated identity — binds the human’s IdP token to the agent at session initiation (e.g. OAuth On-Behalf-Of flow).
Manual/admin assignment — a human administrator explicitly designates an owner in the platform UI or via policy.
Sponsor/succession model — a formal sponsor is required at creation; ownership auto-transfers if the sponsor leaves.
Creation-time attribution — the identity of the creator/deployer is captured when the agent is registered or provisioned.
HR/directory integration — ownership is inferred from organisational data (Active Directory, Okta, HR systems).
Access review/certification campaigns — periodic campaigns prompt stakeholders to confirm or reassign ownership.
Not all methods are comparative of course and rely on different information sources and dependencies within the infrastructure.
There is also a subtle difference between live agents and future-created processes needed to assign an owner at creation time. The current state many organisations are likely to be in, is the former - facing discovery and inventory exercises for agents that are already live.
Let us know your approaches to this emerging problem:
Market Considerations
Many vendors consider ownership as a secondary function - even if they provide the capability. Immediate focus is often on discovery, then authentication, authorization and permission management
Two dominant paradigms exist: proactive discovery vs. creation-time capture - the use of “live” data such as logs, telemetry are used as inference of ownership. Creation capture provides support for the longer-term governance model.
Sponsor model seems most compliant-ready - having a dedicated human sponsor used during agent creation (and in turn provides downstream changes if the human sponsor undergoes changes themselves) seems the most likely to support compliance interrogation.
Linking of human identity provider tokens to downstream agents can provide an end to end level of cryptographic traceability.
Post creation access review campaigns need context - reviewing existing agent permissions and “liveness” requirements really needs an owner to be identified first for them to be effective
Example Vendor Solutions for Agentic Ownership
There are numerous vendors delivering agentic identity solutions. A sample of those have capabilities with respect to ownership discovery and assignment.
Aembit
https://aembit.io/iam-for-agentic-ai/
Aembit uses a ‘Blended Identity’ model that cryptographically combines the AI agent’s non-human identity with the human user operating it at authentication time. It integrates with existing IdPs (Okta, Azure AD, Google) via OIDC/OAuth 2.1 so every access request carries verifiable human context. The human is not discovered post-hoc — they are bound into the access token at session initiation.
Andromeda Security
https://www.andromedasecurity.com/use-case/agentic-ai
Andromeda explicitly offers a ‘Human Ownership and Governance’ capability. It identifies and certifies human owners for each discovered agent, runs ownership and access review campaigns, and enforces least privilege based on confirmed ownership. The platform maintains a centralised inventory mapping agents to humans and supports ongoing certification cycles.
Clutch Security
https://www.clutch.security/use-cases/workforce-attribution
Clutch has a dedicated ‘Workforce Attribution’ use case that reveals every human-NHI relationship — creator, owner, user, or value exposer — for the full NHI estate including AI agents. Its Identity Lineage™ feature aggregates and correlates data from Cloud, SaaS, Code/CI-CD, Vaults, and on-prem environments to build a visual map of origin, consumers, attribution to the workforce (owners/creators), storage, and resources. Shadow AI Discovery surfaces unmanaged agents, and the Agentic AI Governance module controls how agents use and share NHIs.
Entro Security
https://entro.security/platform-ai-agents/
Entro automatically correlates agent activity with human users through logs, code commits, and device telemetry, then enforces ownership via policies, alerts, and automation. Its AGA module uses three data layers — Sources (EDR telemetry, agent foundries like AWS Bedrock/Copilot Studio, cloud environments, MCP servers), Targets (enterprise systems the agent touches), and Identities (human/NHI/secrets) — to build a complete agent profile and attribute each agent to a creator/owner. Ownership is then enforced through access review campaigns aligned with IGA principles.
Microsoft Entra (Agent ID)
https://www.microsoft.com/en-gb/security/business/identity-access/microsoft-entra-agent-id
Microsoft Entra Agent ID (in public preview) introduces a formal ‘Sponsor’ model: every agent identity must have one or more human sponsors, who are accountable for its lifecycle and access decisions. Sponsors are assigned at creation or via the admin centre. If a sponsor leaves the organisation, their sponsorship is automatically transferred to their manager via lifecycle workflows, ensuring no agent becomes ownerless. Access packages requiring sponsor approval enforce human accountability at each access request. The Agent Identity Blueprint also records publisher, roles, and permissions at the type level. Both attended (on-behalf-of OAuth OBO flow, tying the agent to an authenticated human) and unattended (autonomous) modes are supported.
Oasis Security
https://www.oasis.security/product#ownership
The Oasis NHI Ownership Discovery Engine uses purpose-built AI/ML algorithms to suggest and assign owners by analysing the digital footprint and behaviours of those who consume NHIs — without requiring pre-existing metadata, tags, or naming conventions. Its AAM™ product tracks a full chain of custody: Human → Agent → Prompt → Intent → Policy → Identity → Actions → Results. Ownership recommendations are automated and then attested by security teams. The platform also covers ownership succession and flags orphaned agents when creators leave.
SailPoint
https://www.sailpoint.com/products/agent-identity-security
SailPoint’s Agent Identity Security (AIS) product formally certifies AI agents by assigning clear human owner and user accountability, enforcing permissions, and linking agents to the identity context of the users they represent and the data they access. Owners are aggregated from cloud and agent platforms (AWS, Azure, GCP, Salesforce, Copilot Studio) and can have multiple owners per agent. Ownership data is maintained for audit and succession planning — when an owner changes roles or leaves, ownership is quickly reassigned without losing visibility. SailPoint’s unified platform governs human, machine, and agent identities together, enabling consistent access review certifications across all identity types.
Saviynt
https://saviynt.com/blog/ai-agent-lifecycle-management
Saviynt’s view is that if registration establishes the identity, ownership establishes accountability—and without it, governance collapses into ambiguity. Every AI agent must have a named, accountable owner from day one, and that ownership must persist and be enforced throughout its lifecycle. AI agents do not belong to systems; they belong to a human sponsor, a team, and a defined business purpose. This means a specific individual—not a shared mailbox—is responsible for the agent’s behaviour, access, and compliance, with clear alignment to business and executive oversight.
Saviynt identifies owners by leveraging authoritative sources such as HR systems and identity directories to map agents and accounts to real individuals and reporting structures. It correlates access patterns, entitlement usage, and system relationships to infer likely ownership where it is not explicitly defined. These inferred owners are then validated through governance workflows, such as certification campaigns and attestation, to establish and confirm accountability.
Token Security
https://www.token.security/use-cases/establish-ai-agent-ownership-and-accountability
Token Security has a dedicated ‘Establish AI Agent Ownership and Accountability’ use case. It automatically discovers every AI agent (custom GPTs, autonomous services, MCP servers, coding agents) and assigns clear human and departmental ownership to each. Orphaned agents — those without a responsible owner or linked to a departed employee — are flagged, and ownership assignment is enforced. Token’s unified identity graph correlates AI agents, humans, secrets, permissions, and data to reveal blast radius. Intent-based controls (declared and observed agent intent) further align permissions to agent purpose.
Twine Security
https://www.twinesecurity.com/use-cases/account-ownership-integrity
Twine’s AI employee ‘Alex’ specifically identifies orphaned accounts — users/agents that have access but no valid owner — investigates which employee should be responsible for each account, and updates the record with the correct owner. This is an active investigation workflow rather than passive metadata correlation. Alex integrates with existing IGA platforms and improves the efficiency of access certification by providing richer context to managers during reviews.
Other Vendors of Note
Anetac, Astrix Security, Eqty Lab, Knostic AI, Radiant Logic, SecureAuth, Sonrai Security, Teleport
Recommendations
For shadow AI / legacy environments (no existing metadata): Prioritise vendors with AI/ML-based correlation approaches.
For Microsoft-centric organisations: Microsoft Entra Agent ID provides the deepest native integration with existing Entra governance tooling and the most formally specified ownership succession model.
For organisations prioritising cryptographic accountability look to see if vendors support the ability for per-session linking of human tokens to agent access materials.
For organisations with mature IGA programmes look to see if existing access governance can be built upon a foundation of linking agents to human reviewers via additional context
About The Author
Simon Moffatt has over 25 years of experience in IAM, cyber, and identity security. He is the founder of The Cyber Hut, a specialist research and advisory firm based out of the UK. He is the author of CIAM Design Fundamentals and IAM at 2035: A Future Guide to Identity Security. He is a Fellow of the Chartered Institute of Information Security, a regular keynote speaker, and a strategic advisor to entities in the public and private sectors.
Last updated 16 April 2026