Claude Mythos and Project Glasswing: The End of Cyber Security As We Know It?
Analyst Comment
Anthropic recently announced something called Project Glasswing. A partnership with leading technology vendors to improve cyber security. Organisations such as Microsoft, Palo Alto, Nvidia and Cisco were part of an initial consort of 12 companies that have been given access something called Claude Mythos. Mythos is a new frontier model that is not currently available for general release.
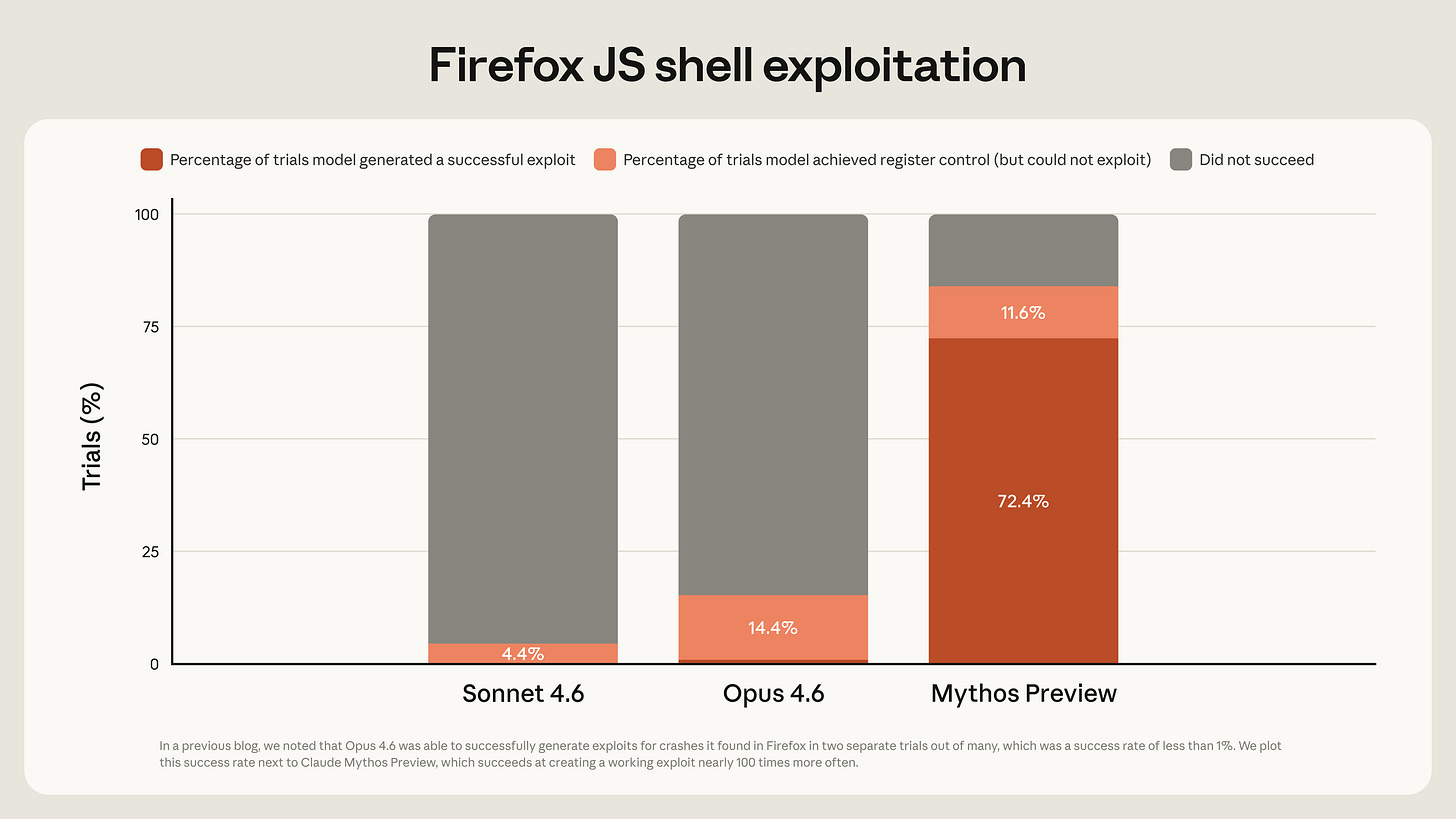
Whilst not created specifically for cyber related tasks, it has emerged at being highly effective at finding and in turn writing exploits against existing software.
Image Source: red.anthropic.com blog
In a blog on the red.anthropic.com site, numerous zero day vulnerabilities were found across a range of operating systems, cryptographic libraries and web applications. Many several decades old. The model then in turn - and often autonomously - wrote exploits against those vulnerabilities. In hours and days.
Why is this important? What impact does this have?
The use of models for vulnerability identification is not new. The interesting aspect is clearly the speed and effectiveness at which this can now be achieved, across a broad array of software platforms and libraries. Human involvement is still there - with scaffolding and prep work, but in reality, once operating, the model will iteratively identify and at times chain together issues that can lead to severe system compromise or denial of service. It is almost like a magic wand pentester.
Anthropic are not making this model available for general release currently - for obvious reasons. They are amassing an arsenal of zero day vulnerabilities and exploits that many providers will take several months to fix. In the wrong hands of course would have significant consequences. I guess in turn, that makes Anthropic a target?
Image Source: Anthropic site
Alas, Project Glasswing is an initiative to take this frontier model and support a defensive position first - by enabling this select first group of technology providers (with 40 others in next level discussion) about how they can strengthen either their own or their clients’s infrastructure.
What are the immediate impacts?
Vulnerability management has become a commodity capability
Triage, Remediation and Response may become an immediate bottleneck
Immediate defensive position may become weakened
Longer term defensive position becomes strengthened
The speed and accuracy of patch code should dramatically improve
Clearly this is a new era in both cyber security offensive and defensive operations - but not necessarily an entire sea-change. As with all technology change, there will be an asymmetric distribution in the usage and in turn benefits. Whilst clearly adversary activity is likely already using existing models in an offensive way, over time the intention (and I believe a realistic one) is that code vulnerabilities reduce from day 0 and in turn future issues will be continually (instead of periodically) identified and in turn resolved before full exploit.
If the majority of adversarial attacks rely upon unpatched systems and zero-day exploitation, that must surely be a good strategic position to take.
AI Generated Summary of Claude Mythos Assessment
The Anthropic Mythos Preview blog describes a step-change in AI capability, particularly in cybersecurity, that signals the beginning of a new era in software vulnerability discovery and exploitation.
1. A fundamental leap in AI capability
Mythos Preview is Anthropic’s most advanced model to date, with major improvements in:
reasoning
software engineering
autonomous task execution
Crucially, its cybersecurity abilities are not the result of specialised training, but emerge from general advances in these core capabilities.
This suggests that powerful offensive cyber capabilities may become a default property of advanced AI systems.
2. From bug discovery → exploit generation
Previous AI models were already strong at finding vulnerabilities, but Mythos changes the balance:
Can discover zero-day vulnerabilities
Can build working exploits, not just identify bugs
Can chain vulnerabilities into full system compromise
Benchmarks show a dramatic increase in exploit success rates compared to earlier models, indicating that AI is moving from analysis → operational capability.
3. The “new zero-day era”
The blog frames this as a shift in tempo, not just capability:
AI can find vulnerabilities faster than they can be patched
Disclosure and remediation processes are no longer sufficient
The backlog of unpatched vulnerabilities becomes a systemic risk
The key change is not just better tools—it’s that AI accelerates the entire vulnerability lifecycle
4. Dual-use risk: defenders vs attackers
Anthropic explicitly highlights a transitional risk period:
Defenders can use Mythos to find and fix vulnerabilities
But attackers could use similar models to weaponise them
This creates a scenario where:
short-term advantage may favour attackers
long-term advantage depends on how responsibly models are deployed
5. Controlled release as a policy response
Because of these risks, Mythos is not publicly released.
Instead, Anthropic launched Project Glasswing, giving access only to:
major tech companies
infrastructure providers
security organisations
The goal is to:
patch vulnerabilities before wider model release
adapt industry processes to AI-driven discovery
6. Implications for cybersecurity
The blog’s core message is that security assumptions must change now:
Vulnerability discovery will be continuous and automated
Exploit development will become faster and more accessible
Patch cycles and validation workflows must accelerate
This is effectively the beginning of:
AI-native cybersecurity—where both attack and defence are machine-driven
About The Author
Simon Moffatt has over 25 years experience in IAM, cyber and identity security. He is founder of The Cyber Hut – a specialist research and advisory firm based out of the UK. He is author of CIAM Design Fundamentals and IAM at 2035: A Future Guide to Identity Security. He is a Fellow of the Chartered Institute of Information Security, a regular keynote speaker and a strategic advisor to entities in the public and private sectors.
Book an inquiry consultation to discuss any of the above concerns.