IAM at RSAC 2024: A review of Identity and Access Management at RSA Conference 2024
This week I had the privilege of being an analyst attendee at the RSA Conference 2024 at the Moscone in San Francisco. This was the second year representing The Cyber Hut as the leading independent boutique analyst firm focused on emerging IAM technologies since we founded - and something like my 6th or 7th RSA overall.
The changes each year in content, the vendors and the problems being tackled is somewhat dynamic to say the least.
IAM the Back Story
Let me take a step back first. I was going to RSA, as always with a primary lens on identity and access management. Now, what IAM looks like in 2024 is somewhat different to what it looked like in 2020 - and certainly different to what it looked like in 2000. IAM is no longer just the LDAP guy (I was that guy) and is foundational to nearly every online event, security control and community engagement platform.
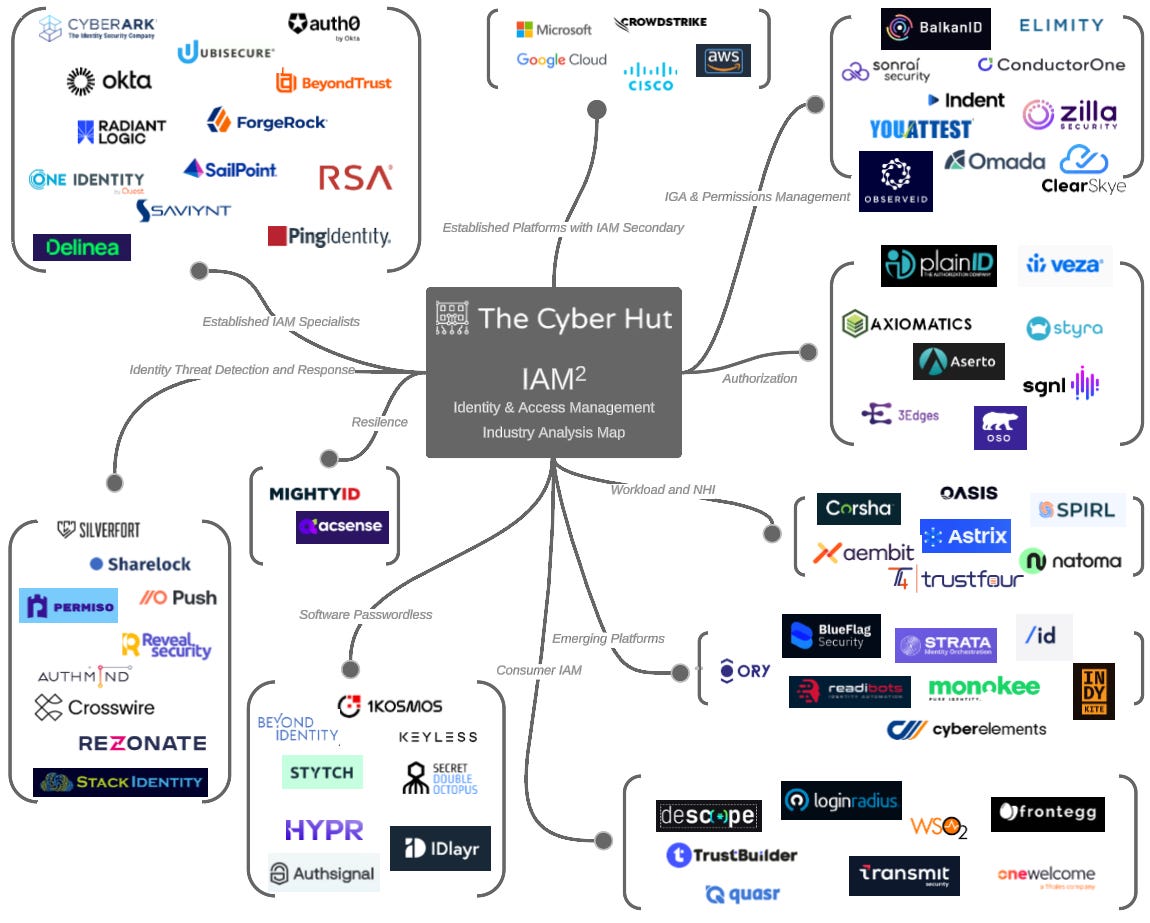
The Cyber Hut takes an evolving view of emerging IAM technologies by tracking about 80 vendors globally that makes up what is known as the IAM Industry Analysis Map - aka IAM2 as we definitely need more acronyms in the cyber and IAM worlds.
The idea behind the map is to get a general picture of momentum regarding what is trendy, what is trending and how IAM is changing. It doesn’t contain every vendor that mentions IAM in their company description on Crunchbase - that comes in at several thousand at a very basic level. The buckets also don’t really reflect on every category known to man - especially not the categories that vendors like to “create” - and is more based on empirical evidence to some degree - what use cases are being solved, how practitioners leverage these technologies and the general vernacular.
Vendor Conversations at RSA
A huge part of my time as an analyst, is of course engaging with vendors and solution providers to understand their offerings, capabilities and use cases they are seeking to solve for the market. Those engagements are “briefings” - and these are primarily one way information flows - that is information coming from the vendor to the analyst. The opposite flow - information coming from the analyst going back to the vendor, is commonly known as an “inquiry” and is a paid for event - and often covers strategy discussion, voice of the customer simulation, market conditions etc.
During RSA week I had 21 vendor briefings, most of which were IAM related - which I feel lucky to be involved with - as seeing the energy and passion of so many talented individuals is a great thing. I have been fortunate to have spent 15 years in the IAM vendor-land - working for startups (Vaau), mid-tier orgs (ForgeRock, Securonix) and global platforms (Sun Microsystems, Oracle) - and I try and have empathy for the often difficult work that vendors have to deal with in those first 2-4 years of existence. From market awareness, funding, product development, early customer support and more.
What Did I Learn?
IAM is hot! Clearly I might say that, but there are some fundamental things happening in the broader IAM space. Clearly IAM is foundational now for several growing concerns. Firstly B2E / workforce productivity has heavily relied on IAM - from basic single sign on, role based access control, authoritative source provisioning and access request and review management - some being driven by compliance, but automating and improving any aspect of that landscape will result in faster employee on-boarding, reduced risk and improved compliance reporting. To that end, there is continual innovation here - both from a startup point of view (Aka Identity) and execution point of (Radiant Logic, Britive, Sphere, Saviynt, Ping, Okta).
Second up is that IAM helps organisations drive revenue - by community engagement and personalised experiences via building consumer IAM platforms for this B2C world - where the C can take on consumers, customers or citizen interactions. Whilst often using the same terms - authentication, MFA, authorization, profile stores, access and SSO - the non-functional delivery is entirely different - as are the success metrics and buying personas. Whilst not a primary topic at RSA there were several vendors with solutions in this space (Okta, Ping).
Now those two “buckets” are quite well understood. Clearly there is huge devil-in-the-detail but innovation is quite incremental and tied to some specific boundaries - namely incumbent technology and budget patterns.
The Emergent Identity-Centric Security Landscape
What is currently intriguing however, are the areas that are somewhat more evolving and dynamic - with respect to integration, value stream and ownership. Here we’re talking more about generic security posture, detection and response, fraud detection and management, workload/NHI risk.
There are numerous IAM focused organisations that use the word security - either in their name, or within their elevator pitch. Why is that interesting? Well the origins of IAM have not been within the CISO organisation. The first world of IAM sat under infrastructure, IT and operations - and ultimately under the CIO - where productivity and cost were important.
As cyber security has evolved however, we’re seeing the first world of the security order (think network, perimeter, firewall, and data protection) having to move both their value position and their integration options. The dominance of cloud, AI, mobile-first and DevOps has altered how security is both deployed and measured. To that end we’re starting to see security providers adding in IAM controls and IAM vendors emerge with a security-first mindset.
Cloud as a Non-Functional Distraction
Before I continue with the IAM + Cyber convergence point, I want to take a little detour to the cloud topic, before I segway back. Cloud is a non-functional. That is, a way to deliver functionality - not a function in its own right. Cloud has however, created a entirely new world of opportunities with respect to service consumption, application deployment and collaboration. However - and it’s a big however - it has created a transient tilt with respect to IAM.
Not all IAM components are cloud delivered - nor will they be. Compliance, control and business process will necessitate the deployment of IAM capabilities as close as possible to the systems consuming those IAM capabilities. If those systems are private-cloud, IAM functions need to be there too.
However, cloud-deployed network and security functions can provide net-new IAM capabilities for the ecosystem they are integrated with. What does this mean? Well look at the likes of Crowdstrike (with Falcon Identity), Cisco (Identity Intelligence), Wiz (with cloud infrastructure entitlements scanning) or Trellix (XDR and threat intelligence) and they have taken on an identity narrative over the past 36 months.
Distributed working, zero trust networking, the need for improved visibility (for attribution and intent management) have driven a requirement to have either a highly integrated identity function, or an assumption that a strong IAM foundation exists. Often the latter doesn’t. More on this later.
Identity-Centric Security
Back to the security and identity mashup conversation. I don’t want to get into the terms war around how to describe this - identity based security, identity-centric security, cyber and IAM mashups - or the argument that cyber and IAM have always been integrated, have never been integrated or never will be integrated. Security orgs using the word identity, and identity startups targeting CISO spend would indicate otherwise, so let’s continue the thread ahead and see where it takes us.
So what does the security narrative give us? Common focus is often on the “protect, detect, respond” pillars from the NIST Cyber Security Framework. Protect assumes that “identify” pillar has been completed - ie we know what we’re protecting. In the network asset world that is a really well known and mature capability set. Apply that to identities and the audience may start looking at their shoes. Why? The world of siloed identity, data isolation, federated systems and offline processing, has resulted in many parts of the identity life cycle being blind to visibility and observability.
Disco For The Win…
Do you know where all identities reside? Who owns each identity? What permissions should they have? What systems are being used? What permissions are being used? What happens to the session post-authentication? Are those user behaviours normal?
These questions on their own have spawned a new set of solutions that are looking to quickly solve this “discovery trap” problem for both people and software. I will abstain from the “workload versus non-human identity” wars by just talking about identity management for software or identity management for people.
Both ITDR (identity threat detection and response) and software-focused identity providers are relying heavily on the discovery phase to enter the client conversation. They are looking to provide the eyes to help figure out what identities are doing, why they are doing it and where they are doing it from. This phase however is unlikely to be paid for in the long term - unless of course the issues being discovered can be resolved. This resolution aspect has a huge long tail of discussion. What are we resolving? Can this be automated? How do we measure the associated risk? This resolution though is where the battle grounds will be drawn, won and lost.
Organisations do not want any more alerts. Again. Still. No more alerts. Organisations are overwhelmed. SoC Analysts are drowning in alerts. Prioritisation is a nightmare. How the resolution is designed, implemented and managed in a sustainable and evolving way will not only improve security resilience but also improve productivity and risk return on investment.
…But Resolution for the Long Term
So what are we resolving? Well this is where the IAM and cyber conversation starts to get interesting. The traditional IAM problem space had (and still has) a few building block problems that nearly always need resolving:
how to remove ghost, orphan, unused identities
how to remove excessive and unused permissions
how to improve authentication assurance
From a security point of view we’re often focused on:
how to reduce the mean time to detection
how to reduce the mean time to recovery
how can we improve coverage and protect more assets
To that end we’re seeing those requirements spill over into both the identity, security and cloud-centric solution provider spaces. For example:
XDR needs identity linkage via session data to help MTTR and attribution
CIEM has evolved to remove ghost data due to CSP mis-configuration
IGA is using co-pilot AI to accelerate excessive permissions removal
Workload/NHI is providing rapid disco to help reduce MTTD
ITDR is mashing threat intelligence with authentication data for MTTR/D
TLDR;
So let’s take stock a little. IAM is evolving to help deliver efficiency for B2E and revenue for B2C. Both of those spheres now have large attack surfaces for adversarial activity, which is being exploited due to visibility and automated remediation issues. Enter stage left detection, protection and remediation tools that are identity-centric - aka ITDR, NHI/workload.
The dominance of cloud-deployed services has highlighted that traditional IAM capabilities were perhaps not designed for the cloud principles of agile, DevOps, speed and modularity. This is resulting in cloud-centric solution providers starting to add in IAM functions for their own customer base - maybe privileged focused, threat focused on a combination.
If security is driven by MTTD and MTTR metrics, and identity becomes a bottleneck to those control points, identity-lite capabilities will emerge organically from this point of view.
So What Happens Next?
An article for “IAM at RSA 2034” is coming - that will guestimate where things will go to for the next decade, which also nudges into the next book I’m currently working on: “IAM at 2034: A Future Guide to Identity-Centric Security” which will uncover a more detailed look at this entire mash of evolution, working against a pattern of Decoupling, Data Centricity, Runtime, Intent and Attribution for both hardware, software and people based identity management.







Author: Simon Moffatt. Get in touch.
Appendix - The Cyber Hut IAM Vendor Engagement List at RSAC 2024
Aembit - Replace manual and insecure workload access with our automated and secretless Workload IAM platform.
AKA Identity - The Data & Intelligence Layer for IAM. AKA simplifies manual and inefficient identity and access management decisions with visibility, intelligence and action.
Astrix Security - Securing Non-human Identities. The Astrix security platform enables you to control and secure API keys, OAuth apps, service accounts and other NHIs, protecting your business and engineering environments from unauthorized access.
AuthSignal - Enterprise grade customer trust without the pain. Authsignal partners with leading brands to balance security and customer experience. We protect airlines, marketplaces and financial institutions by rapidly implementing identity features like passwordless MFA, passkeys and ID verification with minimal engineering lift.
Blueflag Security - BlueFlag Security provides multi-layer defense, protecting developer identities and their tools throughout the software development lifecycle (SDLC).
Britive - The First True Dynamic, Cloud-Native PAM Built for Agility Security that scales as seamlessly as your cloud infrastructure. Reduce risk associated with standing access & over-privileged accounts. Streamline privileged access workflows and remove siloed processes. Enforce security guardrails without slowing development velocity
Crowdstrike - Stop modern identity-based attacks in real-time. The industry’s only unified platform for identity threat detection and response (ITDR) and endpoint security.
MightyID - Protect Your Access to Critical Applications. Bad actors have their eyes on your IAM system. Learn how MightyID keeps your business running in the event of a breach.
Natoma - Non-Human Identity Management. Secure and manage service accounts, access tokens, API keys, workloads, bots and more.
Oasis Security - Manage and Secure the Lifecycle of Non-Human Identities. Oasis Non-Human Identity Management platform empowers security and engineering teams to take control of NHIs and efficiently secure them
Okta - Everything starts with Identity. Identity can create great user experiences, increase customer sign-ups, improve employee productivity, and get apps to market faster.
P0 Security - Secure access in your cloud. Your cloud can be accessed by many different kinds of identities - both human and machine. P0 helps secure access for all identities, without disrupting developer workflows.
Permiso Security - Bad Guys Use Authentication Against you. Attackers have the creds to your kingdom
Push Security - Stop identity attacks. Push is a browser-based agent that detects and prevents identity breaches
Radiant Logic - Radically simple. Use an Identity Data Fabric to Unify Identity Data, Enable Zero Trust, Get Data-Driven IGA, Simplify Compliance, Streamline M&A, Modernize Infrastructure, Speed Time-To-Value. High quality identity data is the key to driving automated governance, enhanced security, and operational maturity.
Rezonate - Protect Identities, Everywhere. Use actionable insights and hyper-security automation to prevent account takeovers and privilege abuse, stop attacks in real time, and streamline compliance.
Saviynt - The Identity Cloud. Turn on visibility, control, intelligence and rapid time-to-value on the world’s leading cloud-native platform, protecting over 50 million identities and counting.
Semperis - The Industry’s Most Comprehensive Active Directory Protection
Sphere - Leaders in Identity Hygiene. Close critical gaps, strengthen your cyber security.
Strata Identity - Leading enterprises trust Strata to migrate off of legacy identity, coexist or consolidate IDPs, add MFA or passwordless to non-standard applications, and ensure resilient identity operations for good—all without rewriting core application code. We call this Identity Orchestration.
TrustFour - Next Generation Zero Trust Workload Micro Segmentation
Transmit Security - The Fusion of Customer Identity Management, Identity Verification and Fraud Prevention Services. Best-of-Breed Services Available in a Single, Modular Platform