Apono Agent Priv Guard, Bravura IAM Insurance Controls, C1 2026 Future IAM Report, Omada new CEO
Plus a round up of Identity Threat Intelligence updates
Strategic & Emerging Headlines
Curated Industry Announcements
Aembit: SPIFFE vs. OAuth: Access Control for Nonhuman Identities
Apono: Apono Launches Agent Privilege Guard, Bringing Runtime Privilege Guardrails to Enterprise AI Agents
AWS: Deploy AWS applications and access AWS accounts across multiple Regions with IAM Identity Center
Bravura Security: What Your Insurer Actually Wants to See in Your Identity Controls
Cisco: Cisco Access Manager: Identity-Based Access Control That Lean IT Teams Can Actually Deploy
ConductorOne: 2026 Future of Identity Report
Entro Security: How smart should your secrets rotation technology be?
Omada: Omada Appoints Jakob H. Kraglund as CEO to Accelerate Global Growth
Google Cloud: Simplify your Cloud Run security with Identity Aware Proxy (IAP)
LoginRadius: Model Context Protocol (MCP): Security Risks Explained
Sailpoint: Launches Shadow AI Remediation
SpyCloud: SpyCloud’s 2026 Identity Exposure Report Reveals Explosion of Non-Human Identity Theft
Strata Identity: Secure Identity for TAK/ATAK at the Tactical Edge
Identity Threat Intelligence Updates
CO-PILOT, DISENGAGE AUTOPHISH: The New Phishing Surface Hiding Inside AI Email Summaries
Under the hood: Security architecture of GitHub Agentic Workflows
Recorded Future: 2025 Identity Threat Landscape Report
Latest On Demand Industry Webinar
Closing the AD Privileged Access Gap
Up Coming Event Attendance
RSAC 2026 - San Francisco - March 23-26
IDSA - Identity Management Day 2026 - April 14
IAM Tech Day - Sao Paolo - April 22-23
Identiverse - Las Vegas - June 15-18
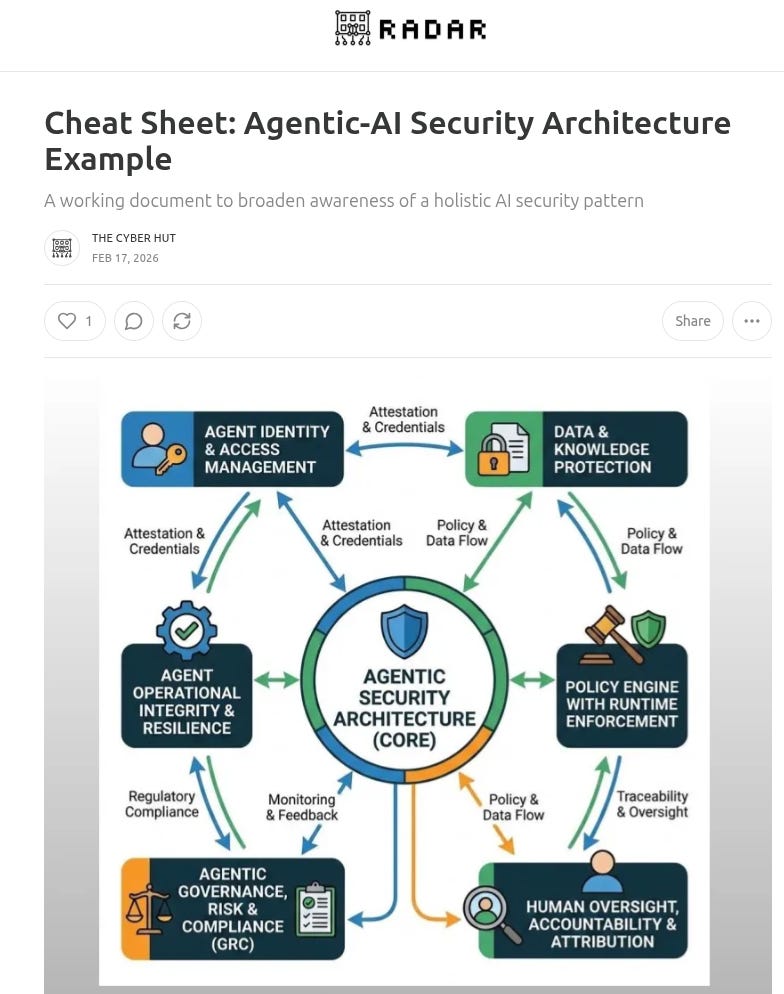
Downloadable Cheat Sheets
Cheat Sheet: Agentic-AI Security Architecture Example
Cheat Sheet: Application Governance
Cheat Sheet: Top 30 IAM Metrics for B2C
Cheat Sheet: Top Metrics for B2E IAM
Cheat Sheet: MCP Security
Latest Identity Security Vendor Reports
A Demo Discussion on JiT for SSH
A demo walk through by P0 Security taking a look at just in time access for SSH services
Latest Podcast Episode
E70 The Analyst Brief: The Rise of AI Browsers. A Game changer for B2C IAM?
Latest Research Report
A Market Guide to Securing the Production Stack
A Fireside Chat with Identity at the Center Podcast
Latest Analyst Insight by The Cyber Hut
The Unified Identity Imperative: Breaking the Cycle of Fragmentation
Enroll. Forget. Reset. Repeat: How Broken Identity Journeys Undermine Identity Assurance
Pre-Emptive Identity Security: Getting Started
“From Operations to Strategic Enabler: Why IAM Must Adapt”
Architecting Identity for a Real-time World
Defining and Securing The Enterprise Production Stack
Latest Recent Industry Webinars by The Cyber Hut
Always On, Always Aware: Building a Continuous Identity Strategy
Identity-First Security for AI Agents with Token Security
Addressing the IAM Data Problem: A fireside chat with Radiant Logic
An Identity Security Playbook: The What and The Why with Silverfort
Putting the AI in IAM a fireside chat with Apono
Too Many IDPs: Why Now, How to Rationalize?
Latest Training Academy Episodes by The Cyber Hut
39: What is Just in Time access and Zero Standing Privileges?
38: How does Identity and Access Management relate to Zero Trust?
37: What is Identity Risk Management?
36: What is Identity Data Management?
35: What are Initial Access Brokers?
Latest Vendor Assessment Report
As assessment of Radiant Logic - analysing their identity-data view of ISPM
Our Recent Vendor Introduction Interviews
Interviews with Stackbob, Reva.ai and Scalekit
What is Teleport’s Agentic Security Framework?
Order IAM and Identity Security Books on Amazon
IAM at 2035: A Future Guide to Identity Security - Paperback, Audio, Kindle and Hardback
CIAM Design Fundamentals - Paperback, Audio and Kindle