Okta and Crowdstrike Earnings Update, Veza+ServiceNpw for Agent Identity, Ping and PAM Plan
Plus a round up of Identity Threat Intelligence updates
Strategic & Emerging Headlines
Curated Industry Announcements
Cerbos: Overcoming IAM blind spots and fragmentation for continuous governance
SecureAuth: Why Your Identity Vendor Is Your Biggest Security Risk
Veza + ServiceNow: The Enterprise Agent Identity Control Plane
Identity Threat Intelligence Updates
AWS Incident Response: IAM Containment That Survives Eventual Consistency
Google API Keys Weren’t Secrets. But then Gemini Changed the Rules
Breaking down a supply chain attack via a malicious Google Workspace OAuth app
Identity Cyber Scores: The New Metric Shaping Cyber Insurance in 2026
Up Coming Industry Webinar
Closing the AD Privileged Access Gap
Up Coming Event Attendance
Orchid Security Community Event - London - March 12
RSAC 2026 - San Francisco - March 23-26
IDSA - Identity Management Day 2026 - April 14
IAM Tech Day - Sao Paolo - April 22-23
Identiverse - Las Vegas - June 15-18
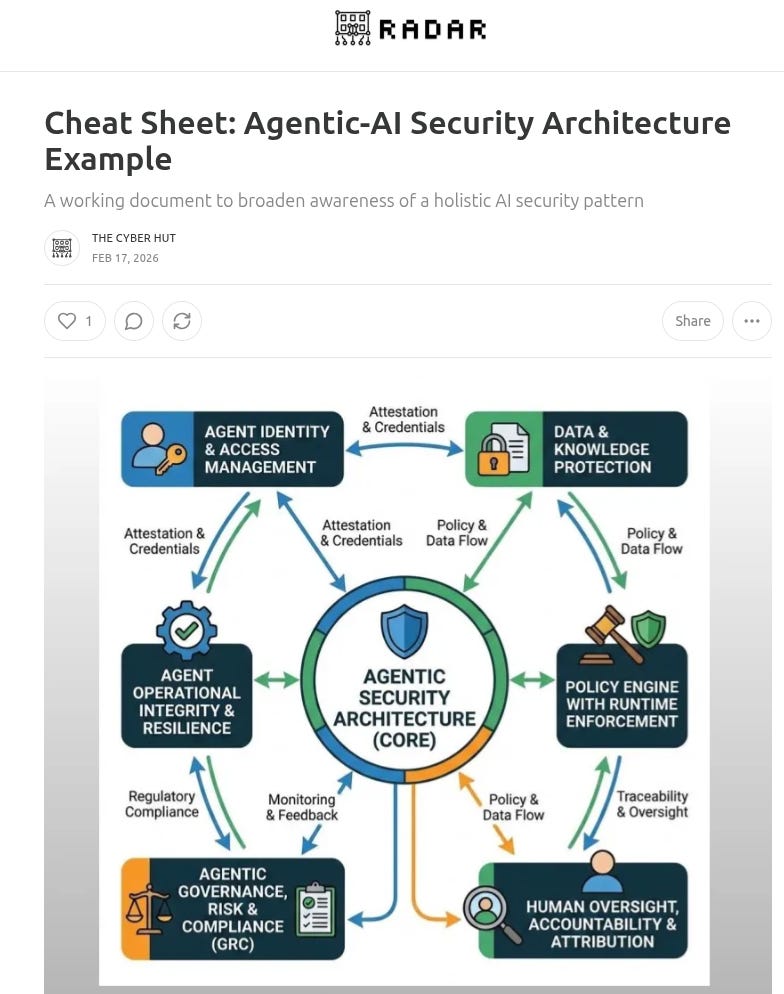
Downloadable Cheat Sheets
Cheat Sheet: Agentic-AI Security Architecture Example
Cheat Sheet: Application Governance
Cheat Sheet: Top 30 IAM Metrics for B2C
Cheat Sheet: Top Metrics for B2E IAM
Cheat Sheet: MCP Security
Latest Identity Security Vendor Reports
A Demo Discussion on JiT for CSP
A demo walk through by P0 Security taking a look at just in time access for cloud service provider components such as S3 storage buckets
Latest Podcast Episode
E69 The Analyst Brief: The Rise of IAM Resilience and Why Semperis is buying MightyID
Latest Research Report
A Market Guide to Securing the Production Stack
A Fireside Chat with Identity at the Center Podcast
Latest Analyst Insight
Pre-Emptive Identity Security: Getting Started
“From Operations to Strategic Enabler: Why IAM Must Adapt”
Architecting Identity for a Real-time World
Defining and Securing The Enterprise Production Stack
Analysing Application Activity
Latest Recent Industry Webinars
Always On, Always Aware: Building a Continuous Identity Strategy
Identity-First Security for AI Agents with Token Security
Addressing the IAM Data Problem: A fireside chat with Radiant Logic
An Identity Security Playbook: The What and The Why with Silverfort
Putting the AI in IAM a fireside chat with Apono
Too Many IDPs: Why Now, How to Rationalize?
Latest Training Academy Episodes
39: What is Just in Time access and Zero Standing Privileges?
38: How does Identity and Access Management relate to Zero Trust?
37: What is Identity Risk Management?
36: What is Identity Data Management?
35: What are Initial Access Brokers?
Latest Vendor Assessment Report
As assessment of Radiant Logic - analysing their identity-data view of ISPM
Our Recent Vendor Introduction Interviews
Interviews with Reva.ai and Scalekit
Latest Video Shorts: Podcast and Interview Highlights
Order IAM and Identity Security Books on Amazon
IAM at 2035: A Future Guide to Identity Security - Paperback, Audio, Kindle and Hardback
CIAM Design Fundamentals - Paperback, Audio and Kindle