Review of RSAC 2026
A retrospective on emerging security trends from the 35th anniversary of the key conference
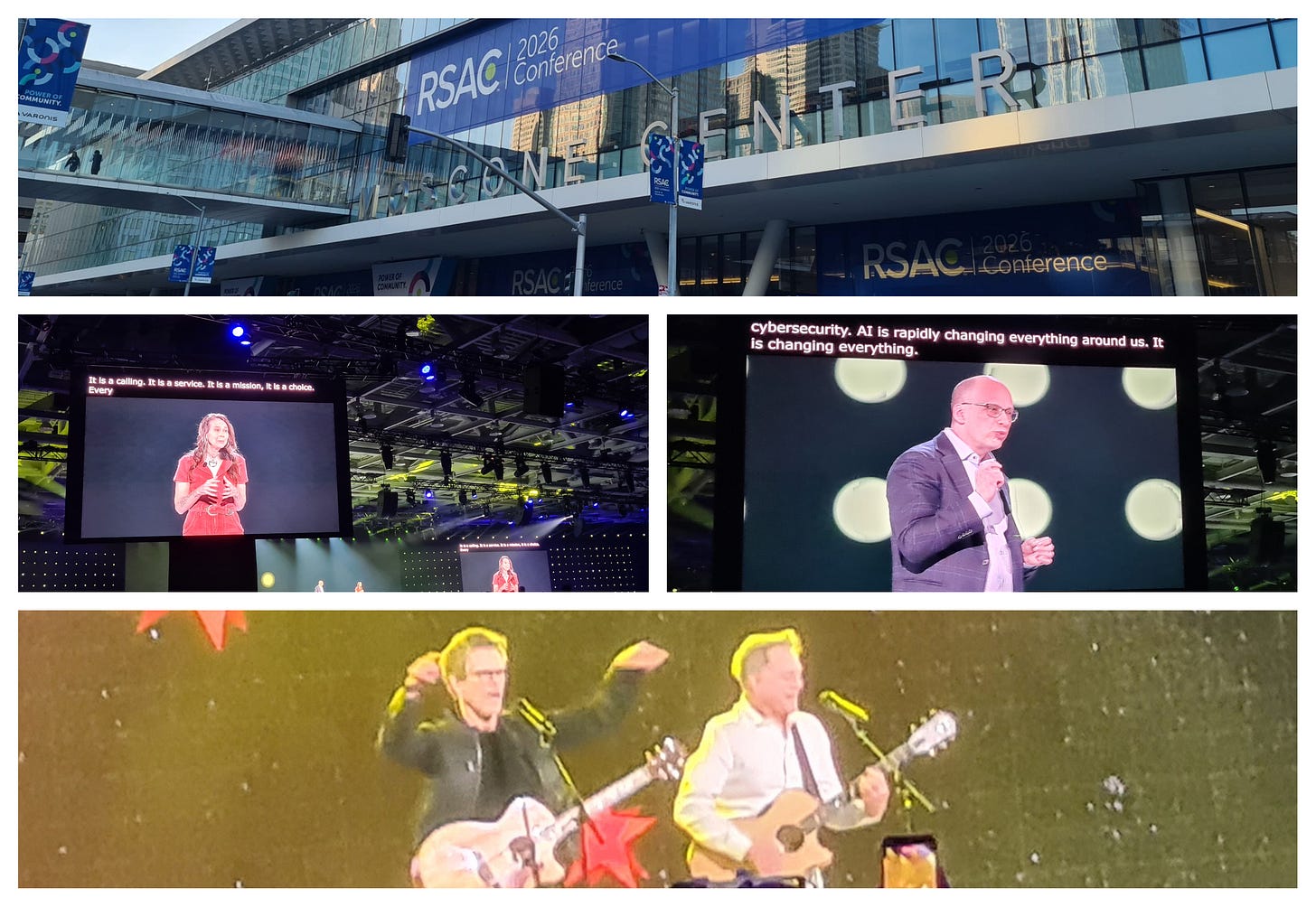
Last week I travelled over to San Francisco for the 35th edition of the RSAC conference. I joined over 40,000 security professionals from around the globe all wondering if AI can be “secured” - by what and how. We got some answers to that during week - for which I will return later - but perhaps that wasn’t necessarily the main question we should have been trying to answer. More on that too.
I have personally being going to RSAC for over 15 years, and this was the 5th consecutive year of taking The Cyber Hut there as an analyst firm.
Even in that relatively short half-decade, technology, world events and business needs have iterated hugely - often going through the entire invention-innovation-obsolescence cycle. I think the biggest contribution AI is currently making, is the significant reduction in time that cycle is taking to complete - which in turn is driving further adoption of AI, but also making the measurable impact more tangible.
Show Floor Splashes
Let’s be clear, if your vendor booth wasn’t “securing AI”, “discovering agents”, “being the AI control plane” your marketing team wasn’t on point. The fascinating thing of course, is that many vendors claiming these capabilities were - 12 months ago - likely to be non-competitive with one another. What does that tell us?
Firstly there is a lot of froth and marketing fluff emerging from many vendors as it pertains to AI security. Secondly, many of the topics that numerous small and emerging technology vendors were trying to solve 12-18 months ago were clearly not attacking the correct problem statements.
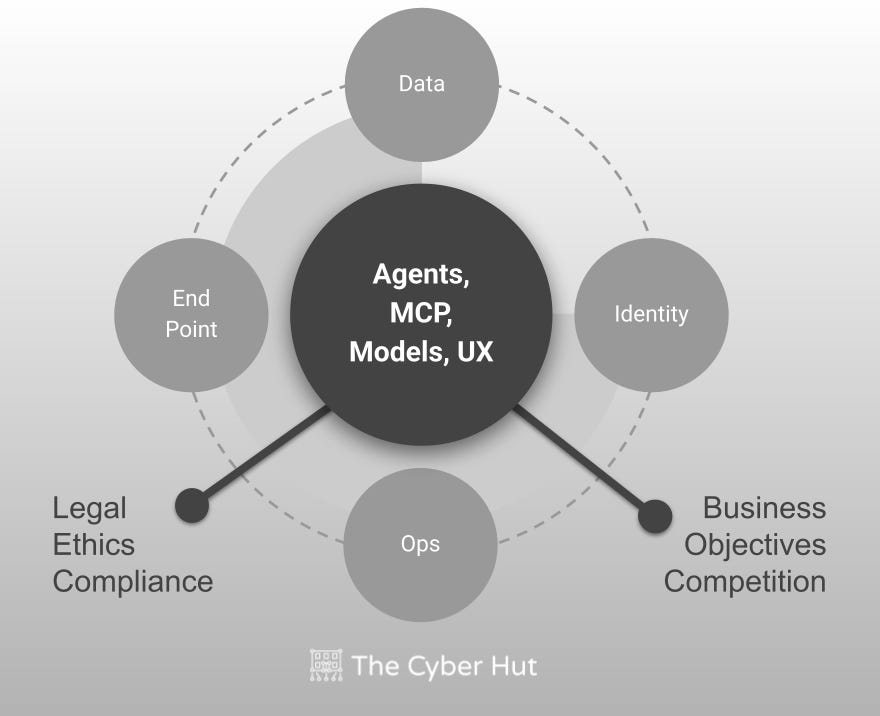
Of course, there are many vendors who are developing some series capabilities to secure the AI world. But not all AI is the same. Firstly AI is hugely broad and equally it will take a “village” to secure both the end to end usage of AI - including the building blocks such as agents, MCP, models and tools - as well as the most critical aspect of all: the thing which makes AI tick, is of course data.
So by association it is quite legitimate to see so many vendors from a broad ecosystem of security to be promoting and gravitating to the AI world. No one single vendor or even platform will be able to handle this complexity today. And I suffix “today” to that statement as things may well change - as a result of the use of AI to the extent that consolidation, feature innovation and understanding, may well allow multiple aspects of the AI world to be secured from a single source.
But we need to first understand AI:
has lots of moving parts
interacts with humans - remember those?
should be designed with higher level objectives in mind
will be influenced by external factors such as ethics and compliance
So the show floor was dominated by AI - from the data, identity, endpoint and operations worlds. These are big broad buckets for sure, but these pillars have many existing concepts that can be applied to the AI world. A few interesting questions and use cases though I feel are not necessarily getting the attention they deserve.
We also need to consider:
How AI links to human actions, ownership and risk
Who or what can access an agent - not just what the agent can do
How to manage the AI-mesh
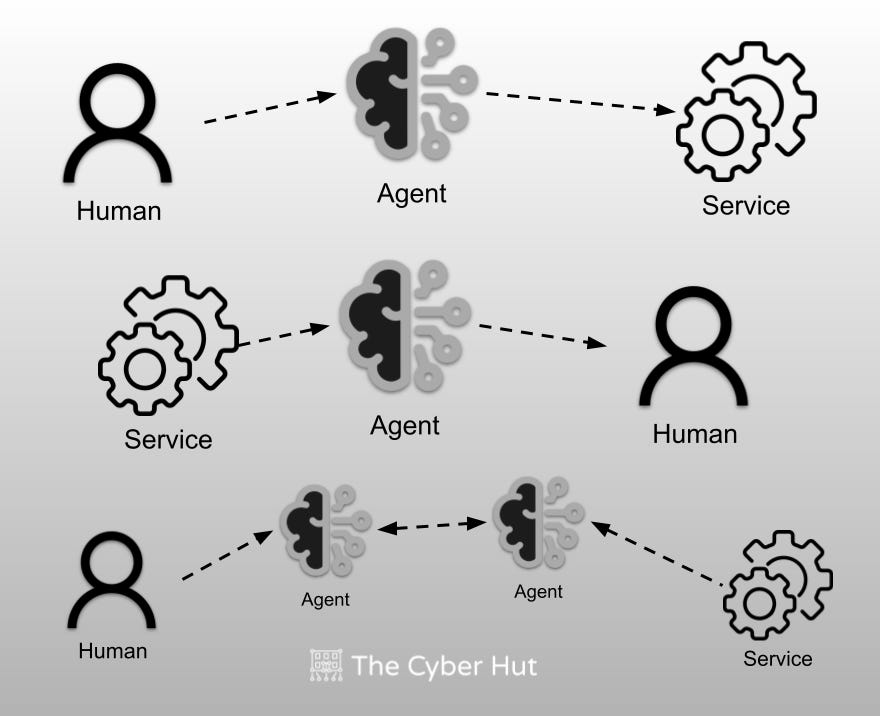
This AI-mesh concept is emerging more and more with the B2C identity world. Typically the modus-operandi for B2C identity is for the service provider to try and deliver personalised experiences for an end user - and in turn be a position to engage more and sell more. To do this of course the service provider requires data - which brings in a privacy conflict (see CIAM Design Fundamentals for why this occurs and how it can solved) and a primary need to “own the user identity”.
The introduction of agentic AI can potentially create a barrier between a service provider and a consumer or purchaser of a service. This was discussed in detail on episode 70 of The Analyst Brief podcast and it will be interesting to see if this does materialise into a real issue.
I guess the AI-mesh may ultimately end up to be a “robot wars” style evolution - with agent to agent being the standard interaction model, which in turn is a race to the bottom with respect to having only AI being the apparatus that can truly interact with and ultimately secure other AI components.
From the show floor, the immediate capabilities that have emerged into relatively stable value points:
Discovery - being able to rapidly find AI components - be that agents running, shadow AI services being used and MCP services deployed
JiT - being able to at least design a just in time access model for agents, so they only have the access they need for a very short period of time
Behaviour - being able to monitor agent behaviour to identify malicious intent, changes in usage or optimization steps that look dangerous or damaging
Ownership - whilst acknowledged as being vitally important, the approach and consistency here for linking agents to carbon life forms is lacking a little
The Cyber Hut Recent AI Research
Topical Talks
Whilst most of my time was in vendor briefings and show floor hopping I did manage to get some live session action in - and as always I tried to select a broad cross-section of topics.
Star Dot Typhoon
My first session, was literally the first talk of the week and a Day 1 0830 start to listen to Inside the Hunt for China’s Typhoons: Disrupt, Deter, and Defend. The “typhoon” campaigns have brought some considerable disruption to numerous private sector entities. These attacks are being attributed to Chinese nation state actions - but with some subtle nuances between Volt Typhoon and Salt Typhoon with respect to attribution, behaviours and more importantly defensive response.
If Salt Typhoon was focused more on espionage and knowledge collection, Volt Typhoon was being classified as “military pre-positioning” and unpicking the why with strong attribution in turn helps defensive actions be more focused.
This defensive response of course relies on threat intelligence sharing - and the link between public agencies and private enterprise and in turn between private enterprises (who may well be competitive in their respect sectors) has been brought up on numerous occasions, with no real solution to strategically improve this. The talk ended with a discussion on the “hack back” option - and whilst this may well be “off the table” with respect to recent US cyber strategy, it generated several audience questions around pro-actively defending core assets.
As an aside, the number one recommendation with respect to lessons learnt was of course identity-centric defense. Not only from an attribution point of (knowing who and what has strongly authenticated) but by analysing account behaviour, permissions usage and the like, can strongly help with intent analysis too.
Drones Need Identities Too
Another talk that caught my eye was entitled Beyond the Fence: Securing Our Skies from the Drone Threat. Whilst this may seem like an obvious candidate for both military and physical related security discussion, it was rapidly boiled down into a cyber and more specifically an identity related issue. Whilst the threat vector has moved from being 2D to 3D - the digital and logical side of drone management has become a major issue.
The rise of anonymous drone activity across many US cities in recent years has sky rocketed - with a lack of both drone identifier information but also lineage of drones to physical people. Sound familiar? It’s exactly the same conceptual use case for both non-human identity and agentic usage today. First discover all instances, then remove anonymous entities and then apply risk analysis functions.
There is a basic “remote ID” concept but lacks integrity protection, is optional and also doesn’t necessarily contain information relating to the physical owner. It would seem the most sensible option to bind the drone to an owner on purchase. Likely via a mobile app with strong MFA. There are numerous existing standards here that could help - from FIDO for authn, but also OAuth2 Device Authorization grant perhaps too - allowing the drone to “act on a user’s behalf”. Preventing the drone from powering on until an owner had been authenticated may not fly (pun intended) commercially but seems like the most sensible way of improving lineage and trust.
Venture Capital + AI = Market Transformation?
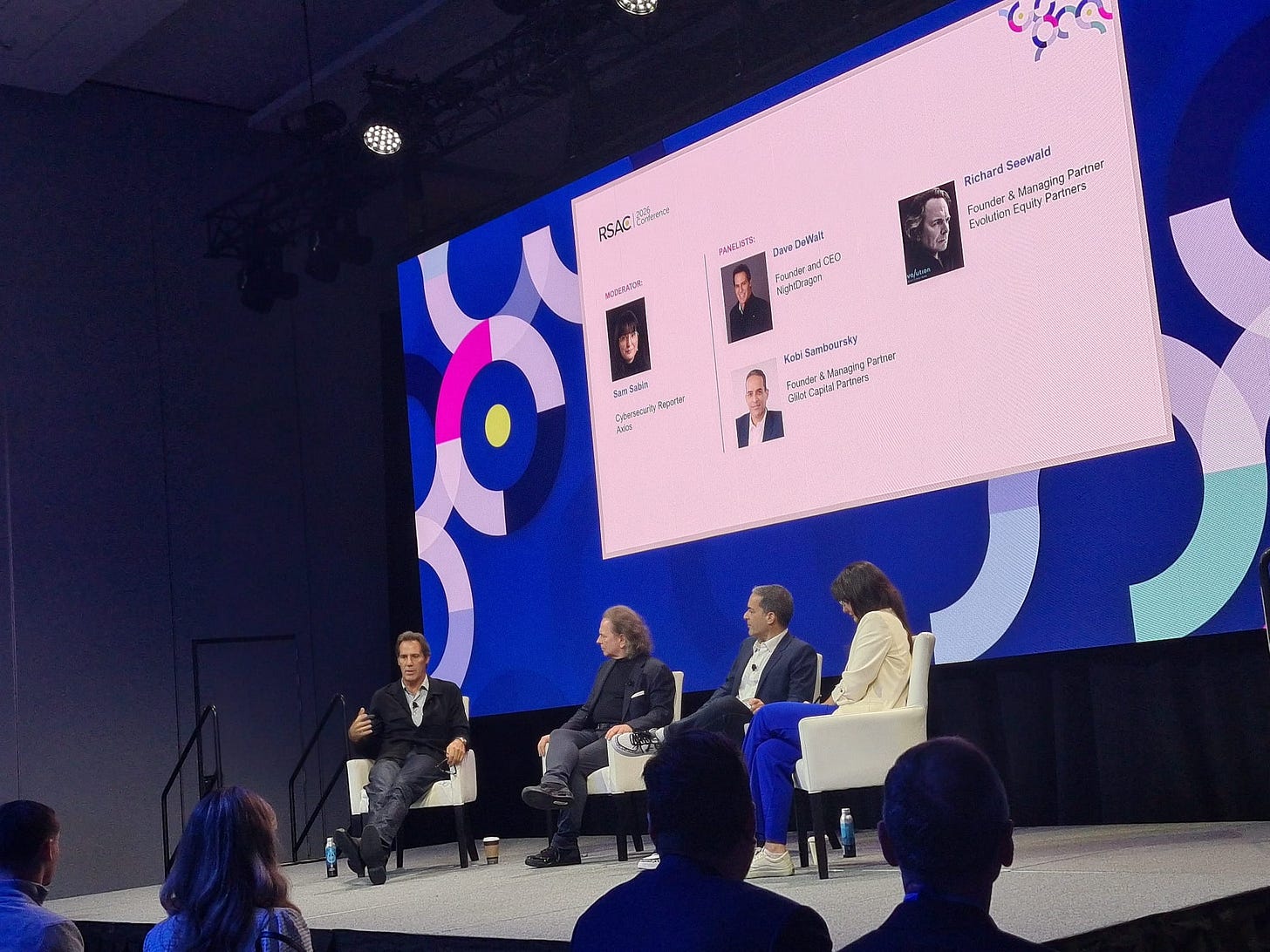
One of the first sessions on the final day brought not only coffee requirements but some insight from the VC and investment world on how they are viewing the AI revolution: what might happen next, how they evaluate AI startups and what might happen to the existing incumbents.
The AI Gold Rush in Cybersecurity: Where Venture Dollars Go was a great panel and the amplification of a “gold rush” is so apt.
The concept of a trillion dollar cyber security company emerged and will AI make this possible? The industry pendulum moves consistently between best of breed and best of suite and will AI accelerate either of these end goals?
Some interesting points were made about how AI is impacting existing market trends - namely that feature implementation and code generation is increasing innovation. So platform providers can rapidly add new capabilities at the edge of their core competency - namely as building stuff now takes less time. That in turn has had a knock on with respect to merger activity. It will be interesting how long that continues for, but for sure, feature differences between organisations is becoming extremely narrow.
But having features alone is no longer enough. The “Balkanisation” of markets and the general anti-American global sentiment is what Dave DeWalt says will be one of the key issues in the coming period with respect to how to get to being a trillion dollar business. How can vendors aim to deliver global services to different geographic markets, with different compliance, sovereignty and supply chain constraints? Does AI help or hinder this?
They also brought up the interesting maturity of companies such as Salesforce, ServiceNow and Mastercard who now have significant cyber security offerings when historically that has not been their core aim. Will this trend continue, with essentially ever organisations providing cyber capabilities at some level?
Midnight at the War Room
The final talk I caught, was literally one of the final sessions on the final day. A distinguished panel of Chase Cunningham (Dr Zero Trust), Sarah Gosler, former Deputy Director of the NSA Chris Inglis and RSAC exec and cyber luminary Jen Easterley dived into the world of cyber warfare.
The panel was supporting and showcasing clips of an up and coming documentary called “Midnight in the War Room” being developed by Semperis. The full documentary will be released in August at Blackhat USA but the panel gave some interesting glimpses into what cyber war in 2026 really means, how it’s evolving and what can be done to respond to it.
The most headline catching line was likely delivered by Chase, articulating that “if your dog is wearing an Internet-enabled dog collar, it’s part of the battle field!”. Meaning that we are now entering an age where digital and cyber warfare is real - and the private sector has become the 6th domain of war fare after land, air, sea, space and cyber.
Innovation Sandbox
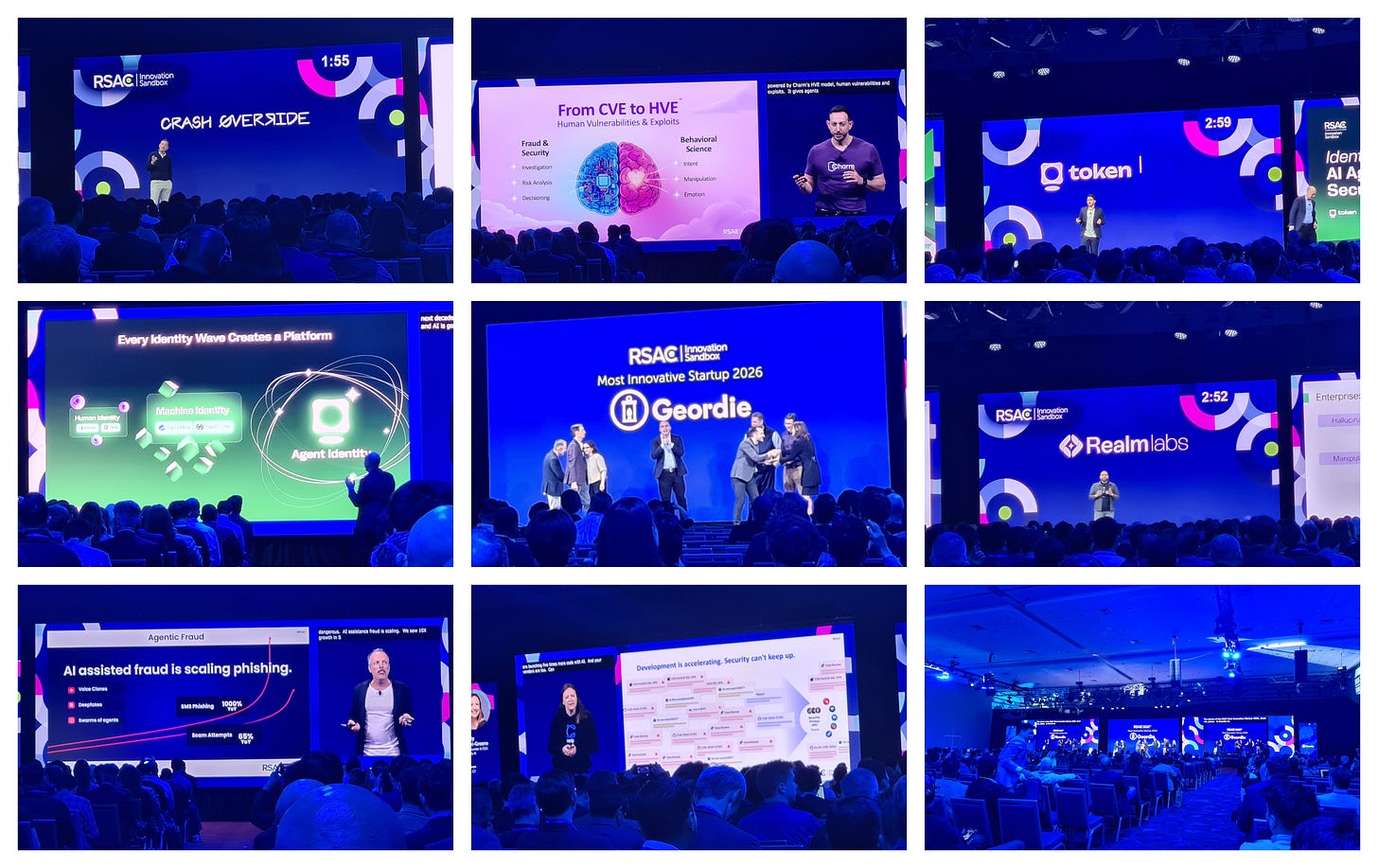
The annual innovation sandbox is a chance for early stage cyber vendors to pitch in front of both an esteemed panel put together by RSAC as well as a few hundred audience members. Each vendor gets exactly 3 minutes to pitch their idea, vision and strategy before being grilled by the panel. An hour or so deliberation results in a winner - with funding and glory - with each of the 10 finalists receiving a healthy $5 Million to boost their growth.
The winner of the accolade of “most innovative startup 2026” went to Geordie AI with their AI governance platform. An end to end view of usage as well as linkage to human ownership were core mentions. They describe themselves as “Geordie gives your organization a holistic, real-time understanding of its agentic footprint, whether agents are locally coded, self or SaaS hosted, or built on low or no-code platforms. Geordie combines behavioral observability and posture context to build a living picture of how agents operate.”.
Numerous startups during the week talked the same talk. Time will tell which wins out.
Other participants included:
ZeroPath - looking to improve app sec scaling
Token Security - improving identity security for NHI and agents
Realm Labs - detection and response for AI with a deep neural scanner
Humanix - improving social engineering detection and response
Glide Identity - reducing login phishing with SIM authentication
Fig - security operations optimization
Crash Override - becoming the control for software development life cycle
Clearly AI - compliance, data and privacy security analyser and assessment
Charm Security - scam and fraud prevention platform using agents
Early Stage Standouts
In addition to both the Innovation Sandbox and the main vendor show floor expo, there is the Early Stage Expo - which is essentially a combination of the two. Around 80 vendors - some entirely new, some with a bit of funding and a year or two in the market - exhibit and engage in prospect discussion. A few that caught my attention from an identity point of view:
12 Port Inc - looking to reinvigorate the privileged access space
Identity Rules - a Mexico based ITDR and identity behaviour startup
Klyro - IGA focused helping to accelerate application onboarding
WideField Security - visibility and behaviour monitoring
Hush Security - NHI and machine security platform
Vendor Briefing Shout Outs
A quick shout out to vendors who I met with more formally to discuss their product, sales and technical go to market updates. It is always exciting to get updates from so many smart and innovative leaders, passionate to help solve some of today’s most pressing identity and cyber security problems. Over the week I spoke with:
Andromeda Security - “Intelligently discover, secure, and govern AI agents, humans, and NHIs—driven by risk and behavioral context.”
AppViewX - “Automate certificate management and PKI. Govern agentic and machine IAM. AppViewX secures enterprises for the AI and quantum era.”
Axiad - “Trusted Identity. At the speed of now.”
Cy4Data Labs - “Unlimited Encryption Keys. Unbreakable Security. Zero Performance Impact.”
Britive - “We don’t manage standing privileges. We eliminate them. One control plane, one policy, every identity.”
Cisco - “Leverage intel from across your stack to enforce policy, manage endpoints and deliver trusted access. Multi-cloud NAC with zero trust makes it possible.”
Delinea - “Redefining identity security for the agentic AI era”
Descope - “Reduce user friction, prevent account takeover, and get a 360° view of your customer and agentic identities with the Descope External IAM platform.”
Entro Security - “Unified identity security and lifecycle across Non-Humans, AI Agents & Humans”
ManageEngine - “Secure and manage enterprise digital identities and
privileged access.”P0 Security - “The P0 AuthZ Control Plane™ makes production access fast, secure and easy to manage. No standing privilege, no manual overhead, no audit surprises.”
Pathlock - “When traditional IGA isn’t enough, companies turn to Pathlock for compliant provisioning, fine-grained SoD analysis, user access reviews, privileged access, and continuous controls monitoring.”
Permiso - “Discover.Protect. Defend. Monitor All Identities In All Environments. Redefining identity security for the agentic AI era”
PlainID - “Agentic AI changes everything, Run-time Authorization makes it secure.”
pQCee - “Be Quantum Ready. Start your quantum readiness journey early”
Unosecur - “Discover, govern, and enforce least privilege for every AI agent, NHI and human identity across multi-cloud, SaaS, IdPs, and on-prem in run-time.”
Crowdstrike/SGNL - “SGNL sits at the center of your IAM architecture. It eliminates standing privilege and instantly adapts access when conditions change.”
Silverfort - “Discover and protect every dimension of identity, everywhere. Human, machine or AI, cloud or on-prem—including systems that couldn't be protected before.”
Teleport - “Teleport unifies identities — humans, machines, and AI — with strong identity implementation to speed up engineering, improve resiliency against identity-based attacks, and control AI in production infrastructure.”
Zluri - “Gain complete visibility into identities and access, automate governance, and continuously manage identity risk across your enterprise.”
Pick of the Parties
And finally…RSAC wouldn’t be RSAC without some legendary parties. Whilst the jeg lag inevitably kicked in, I did manage to float across the evenings to continue the networking, grab a beer and even on one night - shock horror - get away from RSAC entirely and see one of my favourite musicians, the iconic Johnny Marr former guitarist of The Smiths at the fantastic small venue the Great American Music Hall.
A few specific shout outs should be raised. Wednesday I attended the Security Founders' Oasis at the great Chinese restaurant Fang hosted by Leen, Ross Haleliuk (Venture in Security), Caleb Sima (White Rabbit VC), Cimento AI and Paul Lanzi (IDenovate). Really packed party with a broad selection of startups and founder leaders.
Monday I got to attend someone else’s podcast (instead of host The Analyst Brief) for a change and watched a live recording of the Silicon Zombies record an episode called 'The Art of the Possible in Cyber-security' with experts from Acalvio Technologies and accuknox over at the Embacadero Center.
The final night on Wednesday I headed down to Yerba Buena bar for The Hive Reception hosted by Bugcrowd, HPE Networking, Menlo Security, and Unosecur - which should get the marks for the best craft beer during RSAC with a great Drakes Hazy IPA on draught.
After that was the Insight Partners ScaleUp party on Minna sponsored by Veeam, Teleport, Island and Delinea amongst others.
One final party shout out should really go to investors Thoma Bravo for hosting a great event at the Museum of Modern Art. A key highlight is yet another musical one, this time with Kings of Leon entertaining the cyber masses.
Final Comment
From a technology point of view AI dominated. There’s no question. From how it can be protected to how it can be used within cyber. There are clearly lots of unknowns and lots of moving parts, but the innovation cycles are collapsing rapidly. Feature implementation has accelerated hugely. But whilst the “how to build” may have become easier with vibe coding and faster integrations, the “what to build” can still be tough.
As that needs humans. And I think that was a key underlying theme throughout the entire week. Either being explicitly called out in several of the key notes - specifically about the power of the community within cyber - but also more subtly when trying to understand where AI is taking us.
We must not forget the human-aspect within AI and technology in general. How we will integrate and use technology, the benefits (and potential damage) it can bring to us and our actions as responsible and accountable people.
I guess this was brought to a funny pinnacle, with the actor Kevin Bacon (and this brother) encouraging a packed key note audience to become only one-degree away from a Bacon with a mass singalong. Let’s end it there.
Further Resources
About The Author
Simon Moffatt has over 25 years experience in IAM, cyber and identity security. He is founder of The Cyber Hut – a specialist research and advisory firm based out of the UK. He is author of CIAM Design Fundamentals and IAM at 2035: A Future Guide to Identity Security. He is a Fellow of the Chartered Institute of Information Security, a regular keynote speaker and a strategic advisor to entities in the public and private sectors.
Book an inquiry consultation to discuss any of the above vendors.