Review of IAM Tech Day Sao Paulo 2026
The largest IAM event in LATAM
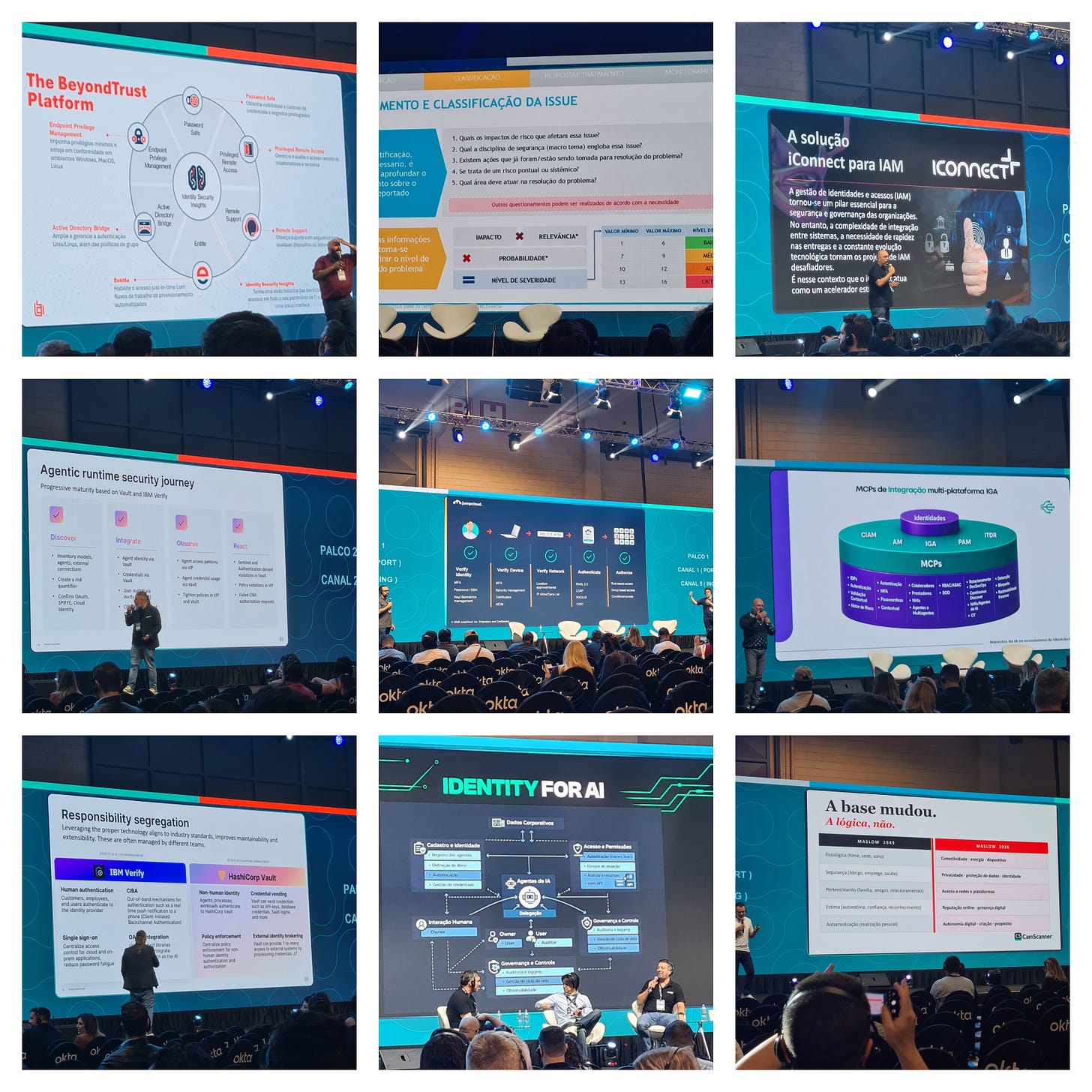
Last week I had the pleasure of attending and presenting at this years IAM Tech Day down in Sao Paulo, Brazil. Alfredo Santos and team have created a great community of identity experts from a broad range of sectors and locations across Latin America.
The 2-day event attracted over 2500 attendees and a strong vendor sponsor list - from large established players to more niche startups, along with numerous systems integrators and consultancies.
Where Is IAM Heading?
I opened day 1 with a presentation entitled “A Dynamic World Needs Dynamic IAM: Where Are We Heading?” - and provided a look into the main research areas we have seen at The Cyber Hut over the past 12 months.
As identity and access management has moved from being a tactical and responsive part of the internal workforce infrastructure, to a strategic enabler that improves productivity, drives revenue and online experiences for B2C ecosystems and integrates with a broad array of cyber security technologies, it has become a major attack vector for adversarial activity. Many would argue it has become the attack vector.
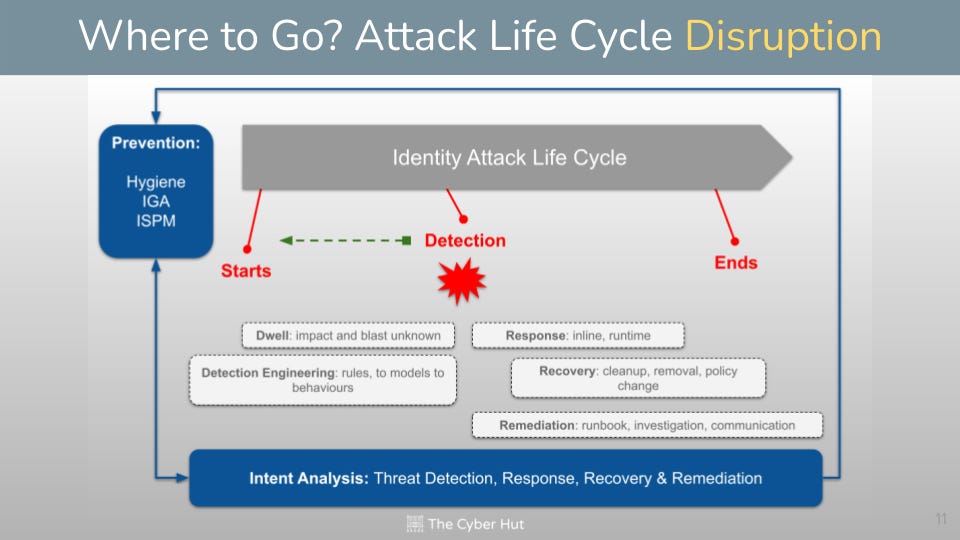
Complex and fragmented infrastructure combined with a highly evolving black market for attack tooling (potentially coupled with AI-based vulnerability exploitation platforms) has lead to a huge spike in identity related risk. That risk is focused at both the identity data layer and post-auth runtime layer too.
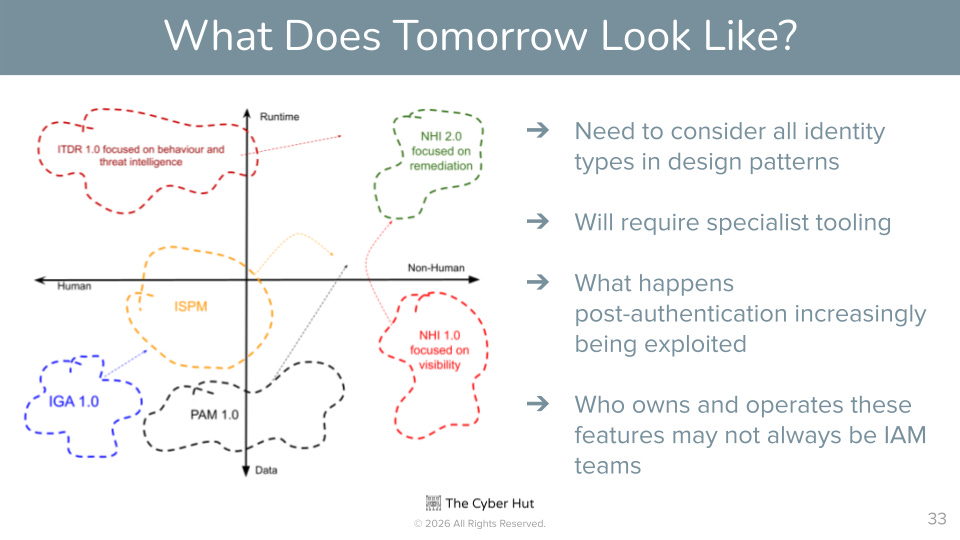
To that end we have seen a new set of technology areas emerge since 2022 that look to improve the security and risk posture of the entire IAM infrastructure world.
At the identity data layer (and with respect to identity data I mainly refer to profiles, policies and permissions) we see a slew of acronyms from IVIP (identity visibility and intelligence platforms), ISPM (identity security posture management) and further expansion of IGA (identity governance and administration) that leads into application governance and AI-governance.
A Future Guide to Identity Security
Available globally on Amazon, in Kindle, paperback and hardback
The strategic focus here is to essentially augment our access request and access review processing with more context - leveraging data sources that already exist within the modern enterprise - and make our decision making smarter. AI is accelerating this decision making too and we’re seeing a range of use cases that improve integration, permissions analysis and policy removal as a result.
From a runtime point of view, we’re seeing numerous initiatives here - including ITDR (identity threat detection and response) and many subtle sub-classes of behaviour analysis. The focus is understanding the intent of an identity - not just making sure they have the correct permissions. This will involve analysing usage and comparing behaviour across-applications. This often requires composite-risk analysis engines - taking into consideration several signals to help triangulate risk and trigger a responsive action.
Understanding when to act is often as difficult as deciding what to do as a response. The response aspect is also evolving and will require more than just a simple allow/deny choice. Disrupting, degrading, redirecting and more subtle response measures are now common - and especially in the external B2C space and aim to deliver security AND usability simultaneously.
A more strategic view of course is not just how to handle the data and runtime aspects of identity risk but do so across ALL identity types. We’re seeing innovation within IGA, ISPM and PAM with the increased usage of generative and agentic AI to improve decision making - alongside expansions into the non-human governance space too.
Ultimately both identity data and behaviour monitoring needs to support non-human, workloads, and agentic-AI as well as both B2E and B2C identity types.
Further Resources on Identity Data Risk
IAM for AI and AI for IAM
Every cyber or IAM conference in 2026 is going to have a heavy focus on AI - either to accelerate IAM adoption or in attempt to secure parts of the AI ecosystem.
Okta started day 1 with a generic focus on how both the LLM and agentic are firstly different components, but also have different control requirements. They articulated that a focus on the “information flows” between assets is a more strategic approach alongside a central plane that looks at both the identity creation flows and the runtime interception and enforcement of permissions.
Sailpoint extended the AI focus, with a need to provide IGA and life cycle management features for non-human identities as well as humans. A key first-principle to that model is to assign owners to agents, workloads and NHIs. This needs to be done for both existing live identities (that are essentially orphaned) as well as imposing sponsors during identity creation time.
Later in the morning, an Okta hosted a panel with ySec and TecPar that looked at AI from a more security exploitation standpoint. The rise of deepfakes, the increased speed of attacks and the ability to craft attacks in a “no-code” way has essentially given the attackers the advantage - for the time being. To that end, AI can be used to help discover the landscape first - what identities exist, where they are stored and what they are permitted to do. It really becomes essential to move from a reactive security standpoint to one that is more pro-active.
eTrust articled that AI is really in its “toddler” years - and emphasised again that using a sponsor and ownership is key to governance (take a look here at our recent Agentic Ownership guide).
Thales - the long time authentication specialists - amplified the story that AI is accelerating login based attacks. From improvements to how attackers can craft phishing emails. Later in the day they also presented a case study where they show how an authentication assessment (internal and external identities versus high and low risk) can help to identify future authentication modality requirements.
Platform providers CoffeeBean discussed how the combination of identity orchestration alongside AI is the strategic way to manage workforce IAM. As B2E has evolved, organisations need to integrate IAM into more systems, consume different data points and be more modular and fine grained with how IAM capabilities are deployed. The integration of logs and activity data can provide a continuous feedback loop into policies and controls. The key is augment existing pillars of IAM capability to improve coverage and usability.
Day 2 saw a panel hosted by NetBR that included practitioners from Itaú Unibanco and Bradesco that discussed how AI can help with IAM but also the controls needed to secure it. From an IAM point of view, access request, IDV analysis and account take over (ATO) protection were prime uses of emerging AI capabilities. The panel also observed how AI adoption is amplifying the need for data protection and how the concepts of external authorization platforms and policy based access control (PBAC) are key parts of that journey.
Identity for Security and Security for Identity
There are very few cyber security technology sectors (think XDR, data, mobile, cloud, network) that don’t either relying hugely on IAM working effectively (which is rarely does) or expect bi-directional integrations for data and runtime tokens and decision making. To that end, there were numerous talks amplifying the security angle of identity - either to protect the IAM infrastructure and its components, as well as the identities, accounts and usage of those components.
Sec4U on day 1 introduced the concept of the “identity attack surface” and how it is increasing. As organisational maturity gravitates to an all-digital approach for staff, customers, services and products, the level of risk increases. As a result, IAM strategy needs to move away from standard joiner-mover-leaver concepts and focus on being continual, continuous and contextual.
A practitioner panel from the airline manufacturer Embraer discussed how security considerations such as intellectual property protection are driving their IAM design. Insider threat, external attacks and complex supply chains can increase risk through visibility blind-spots and a lack of full coverage IGA capabilities. An increased focus on IAM process automation not only reduces error and human effort, it can also allow the organisation to become more risk adverse, by having confidence in the underlying processes. That then allows Embraer to move faster, collaborate and be more competitive. Some tactical comments also emerged, from the need to migrate to just in time (JiT) access to making sure IAM can fully integrate into the security operations centre (SoC) for analysis and investigations.
ManageEngine gave a talk looking at the huge rise in shadow identity - the impact of that and what can be done to tackle it. Whilst traditionally AD-centric, they articulated a broader strategy to improve both IT-security controls adoption and cleanup of the core identity data landscape.
The end of day 1 saw Prove discuss not just security of IAM, but more the privacy of identity data components. The attributes that make up a profile (especially in the B2C space) can be abused as part of identity verification, fraud and PII theft. They articulated the multi-source issue of how identity attributes can be leaked - and in turn used to create synthetic or blended identities that are then used for future attacks and data theft. These false identities can also be used in disinformation campaigns and influence operations that are proliferating into concerns such as election interference. Their solution is provide an identity-graph model that can continuously check identity attribute location and usage, verifying usage, integrity and historical assurance.
B2C CIAM Design Fundamentals
Available globally on Amazon, in paperback and Kindle.
Day 2 saw Banco Bradesco (the third largest bank by assets in Brazil) discuss a case study. Some interesting aspects included the need to future proof against emerging security threats - such as post-quantum readiness and protection against the rise of deepfakes. Identity and security in general is a process not a product and they have developed modular approach to both designing, implementing and deploying IAM components for staff, customers and non-human identities, with composable features for authentication and authorization.
Further Insight and Whitepapers
Raise IT (a partner of Transmit Security) discussed the security and fraud components that are emerging within the B2C CIAM space. Fraud is no longer just attacking the account creation and on-boarding phases, but must be handled end to end at all parts of the B2C life cycle. With the advent of agentic-AI within the B2C world, a transaction signing lineage must be considered that can provide assurance and integrity protection for transactions.
JumpCloud gave a novel description of how device analysis and mobile device management (MDM) systems have evolved into more generic endpoint protection platforms - and must be more closely linked into the privilege access management flows. They argued that identity on its own cannot live in a vacuum and the originating device must be considered during authentication and authorization enforcement checks. Hexnode delivered a similar message later in the day, with their solution offering a broad array of mobile and device integration options in order to strengthen the coverage for device security.
Later on day 2, Silverfort argued that original joiner-mover-leaver processes were not built for security - they were built for productivity and compliance. As organisations move towards a more hybrid deployment model, visibility and control of identity usage becomes a vulnerability. Their view of identity security involves a “runtime access protection RAP” component that can augment and extend Active Directory authentication and access with a range of behaviour and threat detection capabilities.
Recent Industry Interviews
Final Comment
IAM Tech Day is one of the premier identity events globally, not just for LATAM. The core themes of AI and identity security amplified what is happening in North America, EMEA and APAC too.
As IAM becomes a strategic enabler for technology transformation, business productivity and revenue generation, the security and privacy aspects become critical.
How we measure and deploy IAM services is changing massively. Several talks (including those by Shield Security, Sec4U and NetBR) all showcased modern and strategic approaches of how to embed IAM within the C-level talk track. From improved communications and metrics to how to find and in turn manage risk. IAM strategies and tactics need to be co-authored with a broad array of stakeholders. The use of natural language processing as the standard user experience (UX) of choice can open up previously complex IAM policy components to non-technical leaders who can both consume performance data, but also contribute to the overall management of the IAM world.
It becomes critical to work in a top-down model - identifying business and team objectives before identifying the data, cyber and identity components that help or hinder those plans. What does MFA really do for the business? How can just in time access help their partners or customers? These lower level controls must be translated and presented in a way that matters to the key budget holders.
If organisations can achieve that, their future identity strategy will both enable security but also improve usability.
Saúde!
Vendor and Integrator Shout Outs
Authcube - Orchestrate and protect identities in one unique platform what unite security and experience
CoffeeBean Technology - Orchestration in IAM refers to the automated coordination of identity and access management processes across systems, applications, and security tools.
eTrust Security - We are cyber security. We are identity.
JumpCloud - Securely manage devices and access for all human, non-human, and agentic identities.
NetBR - We are an extension of your company, generating knowledge through interaction with your teams , delivering greater value to your identity program.
Prove - Prove transforms identity from a one-time verification event into a persistent foundation of trust-built to verify every person, business, and AI agent, at every interaction.
Sec4U - Your security doesn't have to be complex! Protect your workforce and digital customers without impacting your business flows and usability.
Shield Security - Shield Security has a broad portfolio of services associated with the best manufacturers on the market. The goal is to offer excellent service, seeking to understand the needs of each client for a personalized delivery.
Silverfort - Discover and protect every dimension of identity, everywhere. Human, machine or AI, cloud or on-prem—including systems that couldn’t be protected befor
About The Author
Simon Moffatt has over 25 years experience in IAM, cyber and identity security. He is founder of The Cyber Hut – a specialist research and advisory firm based out of the UK. He is author of CIAM Design Fundamentals and IAM at 2035: A Future Guide to Identity Security. He is a Fellow of the Chartered Institute of Information Security, a regular keynote speaker and a strategic advisor to entities in the public and private sectors.